“Our message to ransomware criminals is clear: If you target victims here, we will target you,” reads the warning from Deputy U.S. Attorney General Lisa Monaco. It’s no idle threat, either—it was attached to a press release detailing the arrest of two people allegedly involved in several Sodinokibi/REvil ransomware attacks.
Ukrainian national Yaroslav Vasinskyi, 22, was one of those arrested. He was allegedly responsible for the high-profile Kaseya attack in July, which injected ransomware into the systems of up to 1,500 victims via Kaseya’s VSA remote monitoring and management tool.
(Editor’s Note: to help protect your organization, ActualTech Media has published the definitive guide to ransomware. Get it here.)
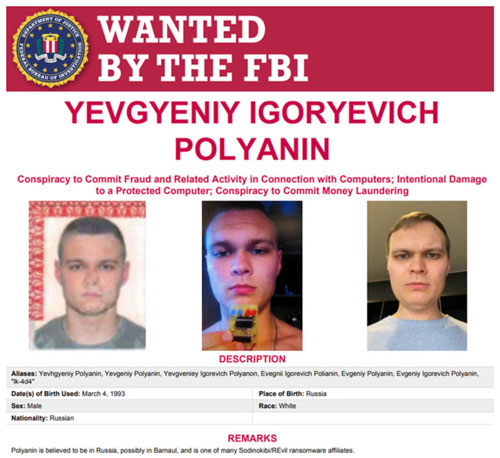
The government action went beyond just arrests. The U.S. seized an alleged $6.1 million ransom payment made to Yevgeniy Polyanin, 28, a Russian national. He’s charged with using Sodinokibi/REvil ransomware attacks against multiple victims, including businesses and government entities, in Texas in August 2019.
Vasinskyi was arrested in October by Polish authorities at a border station while crossing from Ukraine into Poland. The U.S. Department of Justice (DOJ) issued the arrest warrant. According to The Hacker News, Vasinskyi is alleged to have been part of the ransomware operation at least since March 2019. He is accused of deploying about 2,500 attacks against businesses worldwide. Polyanin, according to the most recent information, is still at large.
As part of the Kaseya attack, REvil demanded a $70 million ransom, believed to be the largest ransom demand ever. CRN reported at the time the following message from a REvil website:
“On Friday (02.07.2021), we launched an attack on MSP providers,” REvil wrote on its dark web leak site late Sunday. “More than a million systems were infected. If anyone wants to negotiate about universal decryptor – our price is $70,000,000 BTC [Bitcoin] and we will publicly publish decryptor that decrypts files of all victims, so everyone will be able to recover from attack in less than an hour.”
Things have changed dramatically for REvil recently, however. The cabal was subjected to its own attack, courtesy of a multi-national effort to shut it down. The alliance of cyber-intelligence and law enforcement experts compromised a number of REvil servers—through the common ransomware method of corrupting backups—and took down its network. REvil was also responsible for the famous Colonial Pipeline attack in May 2021.
As of the the time of this writing, there is no public indication that REvil has re-opened for business. However, ransomware actors typically re-form under another name when current operations are disrupted or killed.
The DOJ detailed the charges against the alleged hackers. It’s a frightening statement:
Vasinskyi and Polyanin are charged in separate indictments with conspiracy to commit fraud and related activity in connection with computers, substantive counts of damage to protected computers, and conspiracy to commit money laundering. If convicted of all counts, each faces a maximum penalty of 115 and 145 years in prison, respectively.
That’s serious jail time. It also indicates the increasing seriousness that the U.S. government attaches to ransomware attacks.
