The criminal gang responsible for the Colonial Pipeline ransomware attack in May 2021 got a taste of its own medicine recently, when it was hacked and taken offline.
Reuters reports that the cybercriminal organization “REvil,” based out of Russia, was targeted by a “multi-country operation,” and the group’s website was shut down.
According to the story, law enforcement and cyber-intelligence specialists were able to hack REvil’s network infrastructure, obtaining control of at least some of their servers. Figure 1 shows a message posted on a cybercrime board from one of REvil’s more well-known operatives, 0_neday, describing what happened.
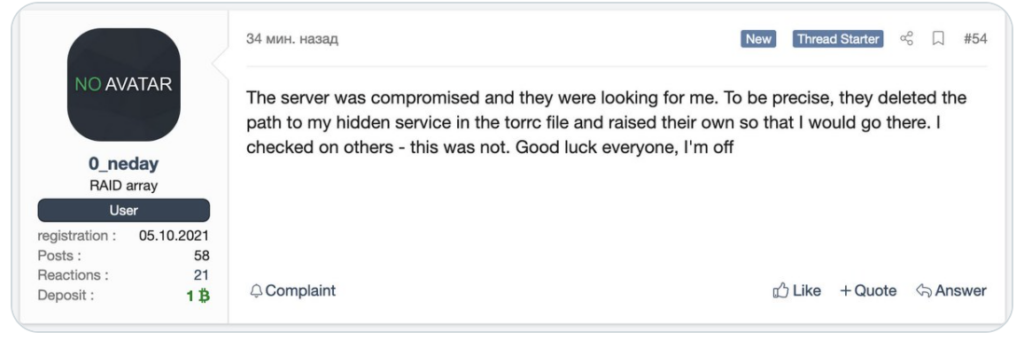
“The server was compromised and they were looking for me,” the message states. He finishes with the statement “Good luck everyone, I’m off”. The message was first reported by threat intelligence site Recorded Future. (Editor’s Note: Recorded Future’s Allan Liska wrote the book “Ransomware: Understand. Prevent. Recover.” for ActualTech Media. Find the book here.)
Compromised Backups Used Against REvil
And in what might be the ultimate irony, it appears that a favorite ransomware tactic was used to take down the servers: infected backups. REvil used backups that were unknowingly compromised by the governmental actors. Those backups, once uploaded to the server, gave the white hats access to the network, leading to the takedown.
Cybercriminals do this as a routine part of any ransomware attack. Ransomware.org’s “How To Prevent Ransomware” page explains how to prevent this from happening to organizations:
“… best practices dictate maintaining current backups for all data and systems in immutable form. Because immutable backups cannot be changed, they cannot be encrypted to lock out access, either.”
The Colonial Pipeline attack got a huge amount of publicity, and caused major problems for the East Coast for weeks, as oil became scarce and gas prices skyrocketed. But REvil is responsible for many high-profile ransomware attacks beyond the Colonial Pipeline hack. They include:
- Meat processing company JBS, which handles about a fifth of the world’s meat supply
- IT management software vendor Kaseya
- Apple. In April 2021, REvil demanded a $50 million ransom that resulted in MacBook schematics being leaked
Because of attacks like these, REvil is high on the U.S. government’s list of criminals that have made a killing via ransomware.
Decryptor Made Available for Free
In good news for others who have been victimized by REvil, the security vendor Bitdefender has created a “universal decryptor” for REvil ransomware, which it is giving away for free. (Bitdefender notes that the decryptor can restore files and recover from attacks made before July 13, 2021, so attacks after that date don’t appear to be affected.)
Bitdefender also warned organizations that this is likely not the end of REvil:
“We believe new REvil attacks are imminent after the ransomware gang’s servers and supporting infrastructure recently came back online after a two month hiatus. We urge organizations to be on high alert and to take necessary precautions.”
The “two month hiatus” refers to July 2021, when REvil shut down for the first time, following the JBS and Kaseya attacks. In early September, REvil was back online and working its, well, evil once again.
