Imagine this: Someone from your public relations team reaches out to you saying they have an email from a reporter asking if your organization was the victim of a ransomware attack. “Of course not,” you respond, “we would absolutely know if we were hit by ransomware!”
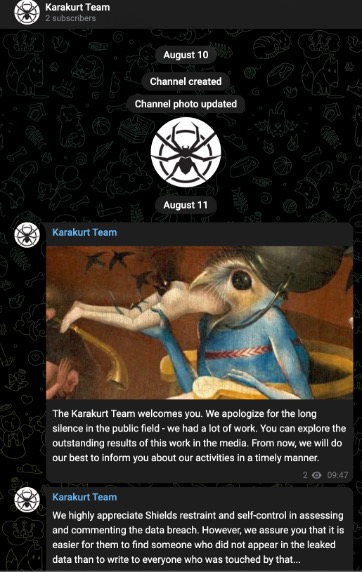
The public relations person then tells you that the reporter is claiming that a bunch of your organization’s leaked data is set to be dumped on the Karakurt ransomware group’s extortion site. You go to their website or Telegram Channel and see it there in black and white: your company data is on a countdown timer (see Figure 1).
How can that be? You haven’t had any data encrypted, didn’t receive a ransom note, and as far as you know, haven’t missed any intrusions. Yet it’s clear that something bad has happened, and you’ve been compromised, even though you still have access to your data and files.
What do you tell your public relations team to say? What steps do you need to take next? Do you need to brief senior leadership? The board of directors?
Organizations are increasingly finding themselves in this situation, including large companies with large security teams, and most don’t have plans in place to deal with this kind of attack. So let’s talk about preparing for an extortion-only attack.
Multi-Faceted Extortion Groups
Mandiant refers to groups like Karakurt and LAPSUS$ that engage in extortion-only attacks as “multi-faceted extortion groups.” These groups use a lot of the same techniques and methods to gain initial access as ransomware groups, but once they have access to the victim network, they simply exfiltrate files and alert the victims that their data will be published if the ransom isn’t paid.
There are a couple of caveats to this type of attack:
- These groups lie, a lot. One way is by claiming they’ve victimized companies that in reality were an incidental part of a another attack. For example, they’ll steal accounting data from a victim and note invoices for a large company among the stolen data. They’ll claim that large company as a victim, even though it was never breached.
- These groups are also notorious for contacting the wrong person in the organization. I’ve seen them send notes to employees who no longer work for the company or who have no idea what to do with the information. In one case, an employee thought it was a phishing test, so they deleted it.
These factors make it a lot more difficult to track these attacks. Unless you can find evidence of their presence on your network, either during the attack or after (take a look at the threat hunting techniques blog post for hints on how to do that), you may not know about the attack until your organization appears on an extortion site.
Understanding the techniques that multi-faceted extortion groups use is even more important than straight knowledge of ransomware-specific vectors, because detecting an attack is much harder. Since most organizations know definitively when they’ve been hit with ransomware, these types of attacks can require more subtlety to detect.
Tabletop Exercises
How would you know if someone stole data from your network? The answer is going to vary from network to network. Some organizations can look at firewall logs for large data transfers; some can look at netflow data to see if data was transferred internally between systems that shouldn’t be talking to each other; still others have data loss prevention (DLP) solutions in place to track those kinds of transfers. Whatever the answer(s) are, it’s important to test those assumptions.
That is where tabletop exercises come in. Hopefully, your organization is already conducting tabletop exercises to prepare for a ransomware attack. In that case, consider adding an exercise preparing for an extortion-only attack.
This will allow you to test your assumptions around detecting not only the intrusion, but the data theft itself. You can use the tabletop exercise to understand:
- Available logs
- Alerting levels, e.g., the size of single data transfer that triggers an alert
- The playbook to use when a data transfer alert is triggered
- Any organizationally specific nuances the security team needs to understand
Ideally, running through the tabletop exercise will help your team make adjustments to logs, alerts or playbooks to better improve your ability to detect data exfiltration. But sometimes even the best detections fail.
When this happens, it’s important to have a communications plan in place to account for notification of an external breach. A tabletop exercise is the best place to test that communication plan. There are many different ways a notification of data posted to a leak site can be delivered, including:
- A reporter reaching out
- A colleague who works for another company notices it and alerts you
- A vendor reaches out to the helpdesk to ask questions
- A client/partner monitoring for third-party risk notifies their contact
- Law enforcement reaches out
- The extortion actor sends the ransom demand to someone not in security
What does the reporting chain look like in each of those cases? Who’s authorized to speak on behalf of your organization and what should they say? A tabletop exercise gives you a chance to test out each of these options and ensure that there’s a solid communication plan in place.
Backtracking
Once you’ve explored the communications plan for an extortion-only attack, the next step is determining how your team will investigate what might have been missed. If you missed the initial entry and the data exfiltration, you’ll need a plan for going back through the logs and determining whether or not the threat actor is telling the truth—and if they are, how to understand the scope of the damage.
I’ve seen a few cases of extortion-only attacks where the initial intrusion was detected and the organization thought they stopped it. By that time, though, the actor had already jumped to other systems using different credentials, so the second phase of the attack was missed.
An important step here is to review logs for any suspicious intrusions, detected or undetected:
- Employees logging into the VPN from unusual places
- Login attempts from unusual devices (e.g., your organization only uses Windows, but someone tried to login using a Linux client)
- Attempted logins from accounts that should have been removed (ex-employees)
- Unusual tickets opened by the helpdesk to reset employee credentials
Your team may have to review these incidents going back a few months. Generally (though not always), you shouldn’t have to review further back than that—the extortion groups want to get paid, so they’ll try to monetize their stolen data as quickly as possible.
Once you’ve reviewed unusual login attempts, the next step is to follow some of the threat hunting steps mentioned earlier, paying special attention to accounts and systems communicating that shouldn’t be.
For example, we often see ransomware groups gain access through third-party vendor systems, such as a server managed by a Managed Service Provider (MSP). The groups will then use the MSP-managed server to attempt to jump to other machines on the network. If that server shouldn’t be talking to other machines on the network, it should raise an alert and be a point of emphasis for post-incident investigation.
Press your knowledge advantage here: the attackers don’t know your network as well as you do, and are going to try to connect to any server that will let them, with whatever credentials they have. Discovering illegitimate connections can help you track down possible intrusions.
Along this line, look for unusual login attempts to your Active Directory (AD) servers. Even extortion-only groups focus a lot of attention on gaining access to the AD (despite the fact that they may not need it if they’re not trying to distribute ransomware). Look for connections:
- At unusual times
- From newly created Administrator accounts
- From servers or systems that shouldn’t be trying to log into AD
Again, these detections will ideally happen during the attack and your team will stop it, but sometimes things get missed. When that happens, plan for the things your team will need to investigate and have playbooks in place for those investigations.
Monitoring
An extortion-only attack can be challenging to detect and even more challenging to respond to, especially when discovered by a third party. One way to mitigate that is hire a service that monitors ransomware extortion sites and alerts your organization when its name appears on one of them. In fact, you may already work with a security vendor that offers this service.
Using a service likes this allows your team to get ahead of these data dumps and implement your response plan before someone else reaches out to you. These services often allow you to monitor for your vendors as well, giving you notification that one of your vendors may have been breached and allowing you to implement a plan of action before that breach impacts your organization.
However your organization chooses to respond, these extortion only attacks are only increasing in popularity, and are something to monitor and develop a response plan for.

