When we think of ransomware, we often imagine a single user’s desktop suddenly hijacked by a ransom message threatening to lock away their hard drive data. The landscape is evolving, however; today, ransomware variants such as Maze and Ryuk attack the victim’s entire network, often via a “back door” opened by exploiting remote desktop protocol (RDP).
RDP, in the simplest of terms, is the most popular communication method by which many users remotely connect to an organization’s servers to conduct work from afar.
An Ideal Attack Vector
RDP is a prime target because attackers keep finding new, subtle, and little-known exploits each day. For example, researchers discovered 25 vulnerabilities in RDP clients during 2020. Even the FreeRDP client packaged with Kali Linux—regarded as one of the most secure Linux variants—fell victim.
Anatomy of a Reverse RDP Attack
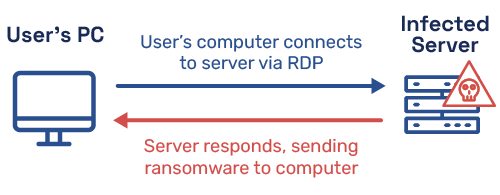
A popular method for exploiting RDP is via a “reverse” RDP attack, which was dissected by Check Point Research in 2019. This is best explained via example (see Figure 1):
- An offsite employee connects to an onsite server via RDP.
- For whatever reason (perhaps the admin slacked on patching), the server is secretly infected with malware.
- Once the user’s offsite computer connects to the infected onsite server, the attacker gains access to the offsite computer by traversing the RDP connection.
- With access granted, the ransomware attack commences.
Figure 1 demonstrates why it’s called a reverse RDP attack: instead of the traditional infected client attacking the server, the infected server attacks the client. In fact, an infected RDP server can take over any and every client that connects to it.
Can You Afford the Risk?
Can you afford to get by continuing RDP usage as-is?
Absolutely not. Due to the COVID-19 pandemic spurring a work-from-home trend that will long outlast the pandemic that bore it, RDP has become one of the most popular solutions for connecting staffers to enterprise servers.
Note also that reverse RDP attacks are not the only threat; far from it. Attacks that simply brute-force RDP services are on the rise as well.
Securing RDP
Take immediate steps to lock down your systems. First, always keep your RDP servers and clients up to date; never connect to an RDP server that is not both fully updated and secured. For example, Microsoft released a patch to address reverse RDP attacks following the aforementioned study.
Second, disable bi-directional clipboard sharing to close off any potential vulnerability related to cutting and pasting data between client and server.
Lastly, monitor and secure RDP with security tools such as an intrusion detection system (IDS), endpoint protection solution, and threat emulation (solutions designed to preempt zero-day attacks).

