QNAP Network Attached Storage (NAS) devices have been hit hard by the “DeadBolt” ransomware, leaving thousands without access to their files. The ransomware was first detected in the third week of January 2022.
The ransom note that victims got demands a 0.03 Bitcoin ($1,100 US) payment in return for a decryption key. The ransom demand says “This is not a personal attack. You have been targeted because of the inadequate security provided by your vendor (QNAP).” QNAP is a major supplier of storage devices for all types of environments.
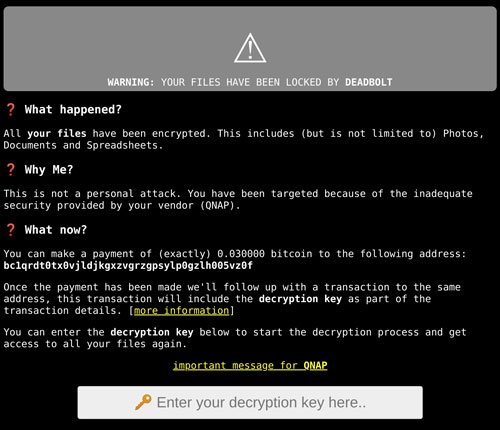
QNAP itself was also targeted by the criminals. The Deadbolt gang said that they would give QNAP the master decryption key to decrypt files for all victims, and the zero-day exploit information used to launch it, for 50 bitcoins, or $1.85 million. It has not been reported whether or not QNAP paid the ransom.
Forced Update
Reports on the number of victims vary, and there seems to of been a reduction in the number of victims a few days after the attack started. This may be the result of a forced update that QNAP released, which shut down the attack vector. Initial reports put the number of victims at nearly 5,000, but following the update, the number was reduced to just over 1,000. (These figures have not been verified.)
The attack targeted Internet-facing QNAP devices. Earlier in the month, on Jan. 7, QNAP issued a news release urging customers to secure their servers. Its first recommendation was to determine whether or not the NAS was exposed to the Internet. It then gave instructions on how to disconnect the NAS, which would protect it.
Attack surface management vendor Censys reported that it found more than 130,000 QNAP NAS devices exposed to the Internet. This potentially puts a great number of devices at risk, although the threat now seems to be minimized.
Some users have reported, on Reddit and QNAP’s message boards among other places, that they paid the ransom, but the provided decryption key either never arrived, or, if it did, it did not decrypt their files.
Incidents like this point to, again, the importance of keeping all your devices patched and completely up-to-date at all times. All those who paid heed to the QNAP warning in early January were safe from the ransomware.
