With the Russian invasion of Ukraine came the deployment of several destructive malware families, known as “wipers,” against entities in Ukraine, with nine distinct variants observed to date. The first two, WhisperGate and HermeticWiper/PartyTicket, masqueraded as ransomware, but they were actually destructive tools rather than legitimate ransomware. This raises an important question: What’s the difference between true ransomware and these destructive tools?
Ransomware Is Financially Motivated
One crucial distinction is financial: The point of ransomware is to make money. When a threat actor joins a Ransomware-as-a-Service (RaaS) group as an affiliate, part of the appeal is the “brand recognition” it offers—association with a known group is beneficial for the affiliate, as it offers victims more of an assurance that they will receive a working decryption key should they pay the ransom.
This assurance is further emphasized as the ransomware group successfully attacks high-profile victims, leading to media coverage. This only increases its reputation, and is why one of the most important aspects of ransomware is the ransom note dropped to the victim’s computer—it provides insight into who’s responsible for the attack and how the victim can pay the ransom.
Let’s look at an example of poorly constructed ransom demand, in Figure 1. While the “ransom note” from the PartyTicket component of HermeticWiper certainly looks the part, it lacks much of the “brand recognition” and professionalism visible in the notes dropped by legitimate ransomware.
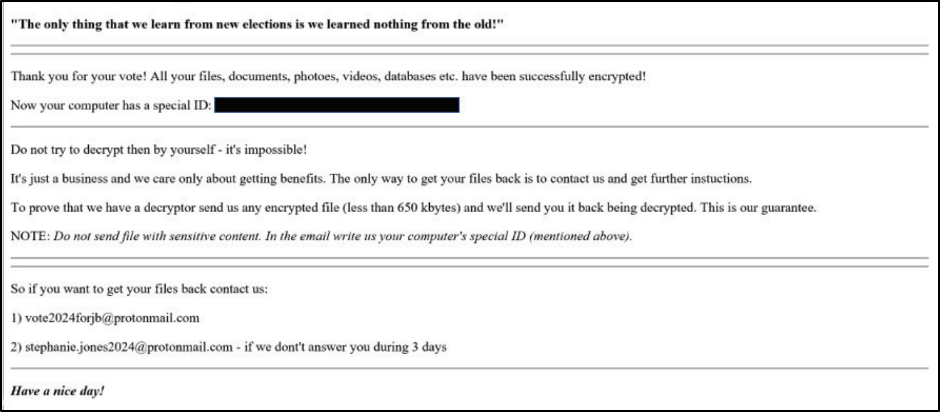
A few things stand out that make this note substantially different from notes normally associated with modern RaaS groups. First, there is no “branding” that associates the note with any particular group.
Generally, this is not how an affiliate of a RaaS would operate; the association with the RaaS is important in helping them get paid, and most RaaS groups feature their name prominently in the dropped note.
To receive a successful payout, it’s imperative for a ransom note to provide proper instructions on how to begin the negotiation. Depending on the professionalism of the RaaS group, they may instruct the victim on what steps should be taken next. These steps usually include how to acquire cryptocurrency, how to contact them, and information about their group.
Higher-profile RaaS groups generally provide an easy-to-use victim chat portal accessible via a Tor-based .onion site, ensuring privacy during negotiation. Some lower-tier groups, such as those that employ spam or pirated software to deploy ransomware, may alternatively provide an email address to contact.
In Figure 1, two politically-themed email addresses are provided, with a vague comment about trying the second one if they do not respond within three days. The political theme and suggestion that a ransom payment would be treated with anything but urgency and professionalism are both unexpected for a serious ransomware group seeking financial gain. Finally, several spelling and grammatical errors are present in the note, which is also uncommon.
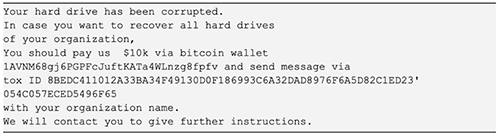
Figure 2 is another example of malware rather than ransomware. This one is a ransom note from the WhisperGate malware shown to the victim as the Master Boot Record (MBR) of their machine is being wiped. Here, another anomaly is observable; the note advises a relatively low, pre-defined amount the victim is to pay, a wallet to which the payment should be made, and a Tox ID to communicate.
First, the technical overhead to begin communication on Tox places a large burden on a victim that would like to negotiate, rather than making the process of paying the ransom as straightforward for the victim as possible.
Next, $10,000 is much lower than the ransom payments requested by most RaaS groups; according to Coveware, while the average ransom payment was down 34% in Q1 2022 as compared with Q4 2021, it was still more than $200,000.
Ransomware Is Opportunistic
Ransomware attacks are opportunistic, meaning they are conducted without specific targets in mind, with the ultimate goal of financial gain. In contrast, both the WhisperGate and HermeticWiper/PartyTicket attacks were highly targeted toward entities in Ukraine, rather than delivered indiscriminately.
This recalls the NotPetya attacks from 2017, which were also highly targeted toward entities in Ukraine, including governments and financial institutions. Eventually, organizations in 65 countries were impacted, but the distribution mechanism for the malware involved an update server for MeDoc, a company that makes an accounting software product used by Ukrainian organizations. This suggests that entities in Ukraine were the intended targets.
Eventually, the NotPetya attacks were attributed to Russian state-sponsored actors. While no firm attribution of the newer wipers has been made, it’s suspected that the malware was again deployed by entities associated with Russian state-sponsored groups.
Ransomware Is a Business
The last thing that characterizes both of these attacks is that the “ransomware” deployed, in both cases, did not function in such a way that would get a victim to pay the ransom requested.
In the case of PartyTicket, the ransomware’s cryptographic code contained a flaw that caused it to generate the same key every time, making the files easily decryptable without paying the ransom.
Researchers suggested that the author was inexperienced in the programming language the malware used (Go) or spent limited time testing it prior to deployment. PartyTicket also identifies specific file extensions to encrypt, including .exe, .cab and .dll files. Many ransomware groups exclude these specific file extensions from encryption, among others, to avoid encrypting files that are necessary for the operation of Windows.
In the case of WhisperGate, the first stage wiper and third stage file corrupter overwrite the bytes of the MBR and filesystem, respectively. Unlike encryption, this operation is irreversible, unless the contents of the files were stored prior to being overwritten.
Both of these examples go against the purpose of the business of ransomware, which is making a profit. While there have been publicly identified flaws in the file encryption mechanisms used by RaaS groups previously, producing ransomware that does not require a victim to pay for the key to decrypt their files is bad for business.
What Now?
When faced with a ransomware attack, one of the last things on a defender’s mind is questioning if the malware is legitimate ransomware or not. However, the purpose of the malware employed plays a large part in how we can, and should, respond to it as defenders. In any case, several general, high-level mitigation strategies are relevant to all types of malware.
Whether a threat is ransomware, a destructive wiper, or another type of malicious tool, general strategies such as logging, employing strong passwords, multi-factor authentication, keeping externally-facing systems patched where possible and phishing awareness are all relevant, as there are overlaps in the tactics, techniques, and procedures (TTPs) employed by different types of threat actors.
Where ransomware differs is the addition of the financially-motivated aspect, driven by the threat of data encryption, and perhaps leaking a victim’s files if payment is not received. Here, considerations like a disaster recovery plan or identifying a ransom negotiation firm, in addition to an incident response plan, come into play. In the case of these destructive wipers, many of the mitigations put in place to address actual ransomware are still effective.

