Ransomware attacks have continued to plague organizations over the past few years, especially with the move to big game hunting at the end of 2019, and the debut of “double extortion” in 2020. Initially, threat actors primarily targeted Windows-based environments, but have more recently expanded capabilities to include Linux-based systems. In 2021, well-known groups including REvil, Conti, RansomExx, and BlackMatter released ransomware specifically designed to target Linux and ESXi, and we expect this trend will continue. Ransomware attacks as a whole are unlikely to abate, and threat actors will continue to improve and expand their capabilities in 2022.
What is Linux/ESXi Ransomware?
Ransomware is a type of malicious software used by threat actors to encrypt a target network’s data. After that has been done, the threat actor will demand a ransom be paid by the victim to decrypt the data. While many ransomware variants target Windows, Linux/ESXi ransomware variants are designed to encrypt those operating systems.
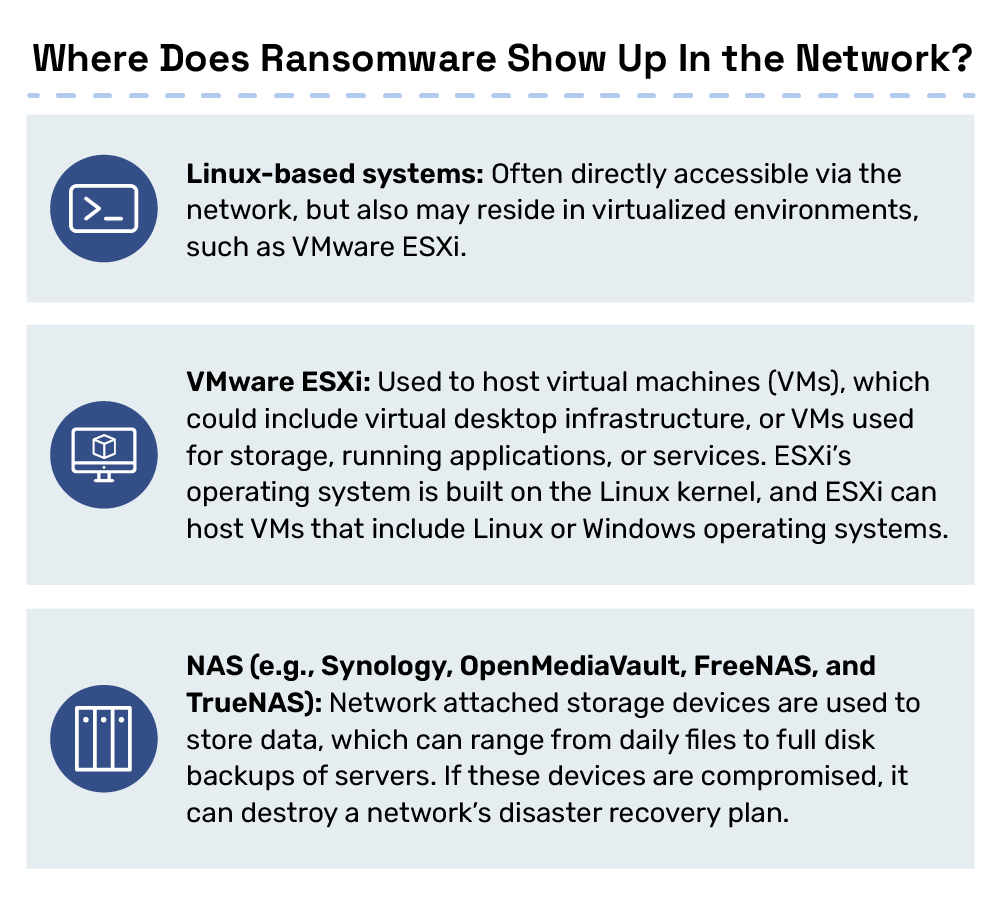
The primary targets of Linux/ESXi ransomware include web servers, databases, network attached storage (NAS) and hypervisors (such as VMware’s ESXi). For many organizations, these systems make up critical infrastructure (see Figure 1).
While one of the first Linux ransomware variants, Linux.Encoder, emerged in 2015, more sophisticated variants did not emerge until much later. In 2020, RansomExx was the first major Windows ransomware variant that was later ported to target Linux systems.
Since then, other threat actors have released versions of their ransomware for both Windows and Linux, often releasing both versions at the same time. These Linux/ESXi ransomware variants have become more prevalent over the last year, as seen in the timeline from Figure 2 below.
Why Does it Matter?
Ransomware threats will persist and continue to evolve, and Linux and ESXi systems present an appealing target for threat actors targeting large organizations. Linux-based systems typically support critical infrastructure that is more sensitive to downtime. They also lack the monitoring capabilities that Windows environments have. Encrypting an organization’s critical infrastructure creates additional pressure on victims, especially those that may not have a sophisticated recovery plan in place that covers their Linux environment.
Opportunity for Damage
Often, organizations use ESXi to deploy VMs, much of which may be critical to running the business. In fact, for large organizations who use ESXi to host the entire organization’s infrastructure–even virtual desktop infrastructure (thin clients) used as employees’ work environments–the encryption of an ESXi hypervisor could destroy their entire ability to operate.
In this case, locking the ESXi servers that hosts the infrastructure is likely more efficient and effective for the threat actor, and ultimately works to increase the damage that can be inflicted on the organization.
For example, there might be several ESXi servers that may be used for different purposes, including hosting the company’s Windows network. While a threat actor could certainly encrypt the individual Windows machines directly, as they often do, encrypting these VMs via the ESXi server might speed up the attack, reduce the possibility of detection by antivirus (AV) engines, endpoint detection and response tools or log monitoring utilities, and encrypt more machines overall.
Speeding up the attack makes it more difficult for the organization to stop the attack midway, meaning that the threat actor will likely encrypt more systems and do more damage. Additionally, machines turned off or offline (or would otherwise be prevented from being encrypted by a Windows locker) will be successfully encrypted if done from the ESXi host.
Finally, AV engines for Windows are well-established, sophisticated and, arguably, very likely to catch a ransomware attack on a machine, whereas the market for AV engines for ESXi and Linux is more nascent.
Understanding the appeal of ESXi and Linux hosts for ransomware threat actors is only half the battle. Next, it’s important to understand how they target these systems and what defenders can do to mitigate the risk to these systems. Here, we’ll look at how these types of attacks start, and some initial steps threat actors could take in victimizing these systems.
Anatomy of an Attack
Ransomware attacks can start with phishing, Remote Desktop Protocol (RDP) brute-forcing, vulnerability exploitation, or the acquisition of credentials for a target network from other threat actors on the dark web.
Often, threat actors will purchase access from other threat actors, known as Initial Access Brokers (IABs), which can include access to RDP-enabled systems, VPN appliances, domain access or Citrix Gateways, to name a few. Additionally, if employees use their corporate devices for personal use (or vice versa), it is possible that they may accidentally download malicious software, and later connect back to the corporate VPN, potentially allowing it to propagate.
While specific details on ransomware attacks are not often publicly available, one aimed at encrypting an ESXi server and its contents could look something like this: Once a threat actor has gained initial access to the network, they might try to get administrator access to Active Directory, which they can then use to get to an ESXi host on the network.
In one instance, a threat actor was able to log in to the SSH ESXi Shell service that was left on by accident. In the same way, when the actor has gained access to the network, they may look for any information that could help them such as network diagrams, reports from previous penetration tests, or passwords stored in the bash history or in files on the system. Along the way, they may exploit vulnerabilities like CVE-2019-5544, CVE-2020-3992 and others (like CVE-2021-21972, CVE-2021-21973, and CVE-2021-21974) to run code on the VMware infrastructure. At this point, it becomes possible to drop the ransomware, and encrypt the ESXi host and its VMs.

What Can You Do?
There are a few steps that defenders can take to lessen the risk of facing a ransomware attack targeting ESXi or Linux infrastructure in their organization.
As VMware advises, there are several steps that can be taken to restrict access on the ESXi host and decrease the attack surface that should be considered. Truesec also has some tips regarding hardware and software configurations that can make an ESXi instance more secure.
While it is often recommended as a way to combat the threat of ransomware, organizations should regularly patch ESXi and Linux systems on the network in the same way that they would their Windows systems.
In addition to securing infrastructure, a well-designed disaster recovery plan needs to be created and tested. Local storage and cloud backups are susceptible to threat actors, if connected to the network. Offline backups should be regularly made and tested with a thorough recovery test.
Ultimately, as we have seen over the past 15 months, ransomware targeting operating systems outside of just Windows, specifically Linux and ESXi, is increasing, and shows no signs of slowing down.

