A critical and often underestimated resource in the fight against malware is the industry’s history of finding and reporting software flaws in everything from big-brand programs to websites and software APIs.
Many software companies and a few larger enterprises run dedicated programs that offer massive rewards for researchers opting for this type of work, sometimes running into the low millions of dollars for discovering really big vulnerabilities.
The terms and conditions of these programs vary, but there is always one rule that every researcher working in this sector knows to take seriously: Any flaws discovered must not be disclosed publicly until the company involved has been informed and given the chance to develop a patch or mitigation within a reasonable timeframe.
That Leads to the Dark Side
Researchers breaking this rule either risk being seen as rogue or, worse, as having gone over to the dark side. A few cross this line, usually to work for a nation state. It’s typically either for money or because they believe it’s in the national interest to do so. However, what all researchers understand is that once that Rubicon has been crossed, returning isn’t easy.
In the kind of strange development seen with regularity among ransomware actors, the well-known Lockbit group wants to make the journey to the dark side a bit easier by setting up its own bug bounty program (see Figure 1). It heralded the program with the headline “Make Ransomware Great Again!”
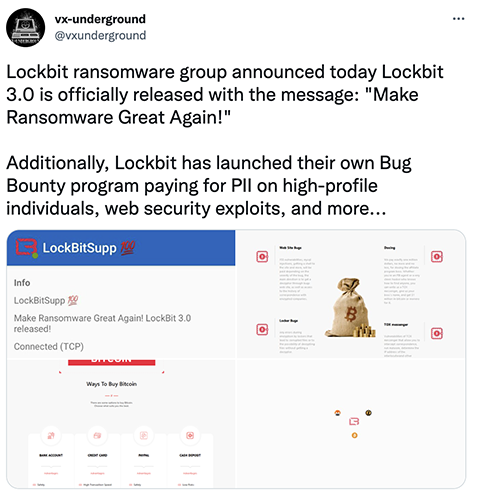
Announced as a new initiative alongside the appearance of Lockbit 3.0, this is a first for ransomware, or for any cybercriminal enterprise for that matter. Enthusiastic researchers are invited to look for bugs in Lockbit’s own malware, including: flaws in Locker itself that might make it possible to decrypt files. The Lockbit group is also interested in:
- Flaws in the Tox P2P messenger app used by ransomware groups
- Flaws in the Tor system that might reveal where a server (including presumably one run by Lockbit itself) might be located
And, for the biggest reward of all, publishing or “doxing” private information harming ransomware rivals:
“We pay exactly one million dollars, no more and no less, for doxing the affiliate program boss. Whether you’re an FBI agent or a very clever hacker who knows how to find anyone, you can write us a TOX messenger, give us your boss’s name, and get $1 million in bitcoin or monero for it.”
Unethical Hackers
It’s unlikely Lockbit will get many takers, not simply because accepting such an invitation would be illegal in almost every country, but because the vast majority of researchers are ethical individuals who wouldn’t consider such work.
But it might also be a mistake to underestimate the potential of criminal bug bounty programs.
Although bug bounty programs have expanded rapidly in recent years, many organizations still operate on an informal basis. Researchers often complain that reporting flaws can still be a thankless and time-consuming chore, and one that doesn’t make them rich.
Interacting with criminals might be a lot easier. With no bureaucracy to deal with, reporting is a financial exchange and nothing more. If setting up a bug bounty program makes it easier to communicate with criminals, Lockbit’s bug bounty program might not be the last we hear of the idea.

